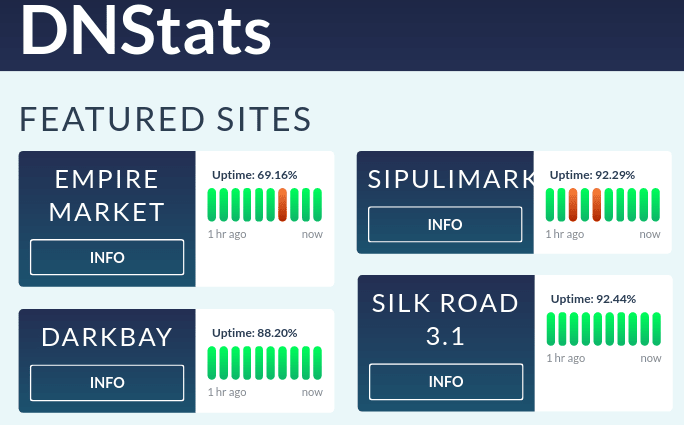
DNStats.net went down in history as the first uptime monitor for onion services that was accessible to the general public. Darknet users knew that this resource was one of the few credible providers of dark web market mirrors. It used to be a firm favorite among market buyers, researchers and even police officers. Yet in 2018, things suddenly went wrong. The good old DNStats unexpectedly started shilling and redirecting users to fake markets. From this review, you’ll get to know how the story unfolded.
Please mind that this article was written about DNStats.net. You might come across some other resources whose names sound similar — but they won’t be discussed in this text.
DNStats Reddit Announcement
In mid-Spring 2014, a Reddit user /u/select1on announced the launch of DNStats.net on the /r/darknetmarkets subreddit. Follow this link to check an archived version of that piece of news.
Back then, this information didn’t cause a sensation at all. Nevertheless, it took DNStats very little time to become one of the most reputable resources with marketplace mirrors and uptime information. Today, there are too many look-alike uptime monitors and news resources of this type. Instead of generating unique content, their copy it from elsewhere and paste with little or no editing.
It would be fair to say that in this sphere, supply exceeds demand. When you want to find a working mirror of a certain darknet marketplace, it should take you less than one minute. And you can be sure that you’ll discover numerous phishing sites on your way too.
Yet in the mid-2010s, there was a completely different situation. The number of sites for finding mirrors or checking the news on the clearnet was limited. In 2014, DNStats came as a revelation and we shouldn’t underestimate its importance for the Internet environment of that decade.

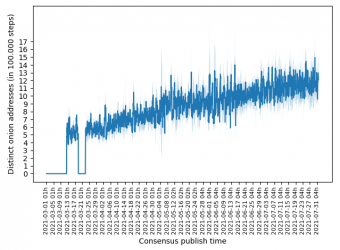
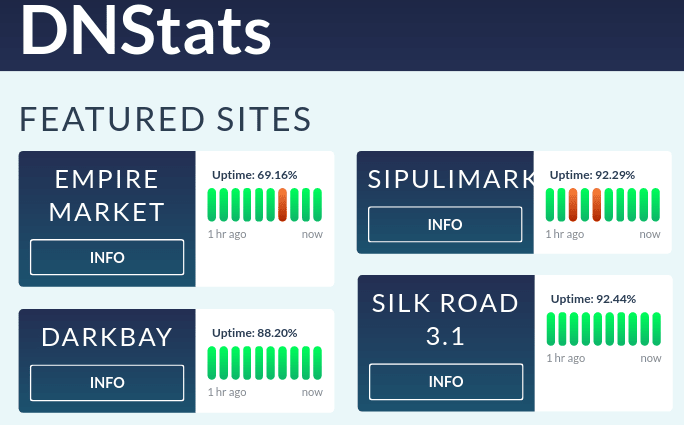
This screenshot shows the looks of the original DNStats.net after a redesign
In late 2011, the Silk Road subreddit was launched. Next year, Eileen Ormsby covered this marketplace in “All Things Vice“. By the end of 2013, DeepDotWeb and /r/darknetmarkets were launched. In a few months, DNStats and Grams saw light — and both were rather innovative for their time. The former, as was already said above in this article, provided marketplace mirrors and historical uptime data. The latter had search, Flow, Helix, Helix Light and Infodesk, to name a few.
To explain the significance of DNStats to its audience, we should probably use a comparison. For the audience of Agora Market, it was just as important as Dark.Fail was to people who used Empire Market. The /r/darknetmarkets subreddit referred users to DNStats to check market uptime and Grams to check vendor profiles and data.

DNStats used to list the lifetime availability of multiple marketplaces
There were times when you would see the Dark.Fail link in the /r/onions subreddit’s sidebar. Then, it was replaced by the link to DNStats.net.

/r/darknetmarkets and DNstats left, /r/onions and Dark.fail right
DNStats Phishing Scandal
The previous admin of DNStats was a person with an impeccable reputation who had hardly any nefarious motives. Unfortunately, the individual who is supervising DNStats now pursues other goals. In late 2018, the design and functionality of the once-reliable project changed dramatically.
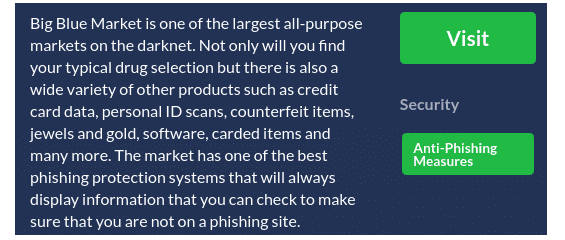
This is a screenshot of the new DNStats
If you try to dig a bit deeper, you’ll be unlikely to discover any valuable facts or reminiscence about the service. The good thing is that the current version of DNStats indeed features a few listings that display uptime information. But you’ll be able to see it only if the last hour is available. So the service is not as useful as it could have been. And alas, it’s not the only problem with it.
The most blatant issue is that the new DNStats displays phishing links that lead to fraudulent marketplaces and other overt scams. One of the most vivid examples is the listing for Escobay. The team behind it copied the CannaHome interface, so this platform might look like a market at the first sight. Moreover, Escobay tries to load some assets from a defunct CannaHome onion address. But in fact, it’s not a marketplace at all.
These days, you might come across weird links on DNStats. They lead to web resources that seem to have been launched yesterday. The lack of history is not a tell-tale sign of a scam but it creates a dubious situation. If only dicey sites refer to any onion service, users might start to ask rightful questions about the credibility of all parties involved.
BlackPass Market as well as a few other listings are mirrored by only other resources with a bad reputation. These resources got notorious for misinforming their audience and promoting scam projects.

DNStats left, another scam project of this type on the right
As for the legitimate darknet marketplaces, DNStats lists them too. But it is much more focused on their fraudulent counterparts. Basically, the situation is the same as on Dark.fail.
Besides, you shouldn’t 100% trust the descriptions for the listed markets. DNStats often shares wrong facts and value judgments. It might say that a certain platform is large and versatile — while in fact, it might be rather small and dedicated to one or several particular types of products.
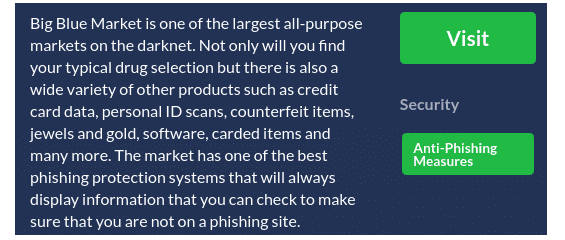
DNStats characterizes Big Blue Market inaccurately, thus misinforming its users
Is DNStats Legit at all in Its Current Version?
Based on the Archive.org data, we can see that it took DNStats around one year to transform to a newer version. The conversion began in mid-Autumn 2018.
The new administrator of the platform got rid of all remainders of the DNStats that we liked so much. He or she placed referral links to Wall Street and Dream markets on the main page. A search of these links gave no results.
WallStreet: wallstyizjhkrvmj\onion/signup?ref=696125
Dream: lchudifyeqm4ldjj\.onion/?ai=3055844889
And that was just the first step on the long way to degradation. The loyal audience of DNStats quickly guessed that the previous admin was no longer in charge of the site. Some people were smart enough to pay attention to meaningful detail.
The last update of Whois records took place in 2017. That was months before DNStats began to deteriorate. This fact might prove that the initial administration never sold or transferred the domain to a third party. Consequently, the new admin seems to have legitimate access to the platform. Alternatively, they might have stolen the credentials and used them to modify the DNS settings.
On October 28, 2018, the new admin switched from Njalla to Cloudflare.
This was the initial state of things:
- 1-you.njalla.no
- 2-can.njalla.in
- 3-get.njalla.fo
And these are the new nameservers:
- peyton.ns.cloudflare.com
- gail.ns.cloudflare.com
Some day after September 27, 2018, the old admin deleted his or her Reddit account. The last post on Twitter was published in July 2018. People who wrote emails to the publicly listed DNStats address never got any response. In August 2018, the DNStats donation wallet (1DNstATs59JANuXjbpS5ngWHqvApAhYHBS) sent BTC to an unknown recipient for the last time.
On October 28, 2018, the DNStats mx servers switched to Yandex — previously, they relied on Google Mail. As you remember, that was the day when the transition from Njalla to Cloudflare took place. Before that, DNStats hadn’t relied on the services of a webmaster. It hadn’t used the search console to verify TXT records. But suddenly, it got both.
This is the Google Search console TXT record from February 15, which was the latest update:
google-site-verification=llUZYZIo8TikibwXwiDTe_KeK95ypw1kOeBDCIIOx4
Here is what we see in the Yandex TXT:
yandex-verification: 2ee10da105953c18
What we know for sure is that DNStats is alive and kicking. Its DNS records were tweaked. Someone keeps sharing Department of Justice press releases on the news page. Some time ago, the site warned its visitors about the Apollon Market exit scam.
There is a referral link to Empire Market on DNStats — and it might give hints on the new administrator of the site. The description of the market features this link twice. The curious thing is that DNStats seems to be the only indexed site that offers this link — and it’s a phishing one.
empiremktw5g6njb\.onion/ref/760948
However, you can find that link if you type “/ref/760948” in the DuckDuckGo search bar.

This is what you’ll see when you try to search for the Empire referral through DuckDuckGo
If we analyze the uniqueness of texts on DNStats, we’ll see that all the marketplace descriptions were purposefully created for this site. They often contain mistakes and misprints, which means that they might be written by the same person each time. Such misprints are not typical of any other site. But when the administrator writes news pieces, he or she copies them from the USAO press releases.
The overall impression is that the person who is in charge of DNStats now has certain expertise in frauds. Most likely, he or she has gained experience on some other sites of this type before. DNStats doesn’t closely resemble any other resource from its sphere, which is a bit weird.
We can suspect that the new admin of the site used to work for the old one for some time. At the beginning of 2015, /u/select1on shared a job offer for a person who could carry out some research on dark web sites. That offer was very concise and lacked any details. It’s hard to say whether the employer managed to hire anyone then. But even if they did, they might have refused to share admin credentials with them.
In summer 2015, the old admin openly confessed that he or she had hired a developer to handle the database. Maybe, not one person but several professionals got access to the DNStats infrastructure. The administrator didn’t specify whether this helper or helpers worked with all the infrastructure of the site or just a part of it. Today, we might assume that a hired person became the new owner of the site. Yet we shouldn’t completely exclude another possibility: what if it’s the same old admin?
Just Sharing Some Guesswork
This is just one of the numerous theories whose authors try to explain what happened to DNStats. Maybe, the old administrator of this resource decided to disappear from the public eye for some reason. He (or she) posted his (or her) last tweet in July 2018. Three months later, they deleted their Reddit account. In August 2018, they transferred BTC to someone for the last time. By that moment, people had sent a total of 28.30143634 BTC to the DNStats donation address. At the current exchange rate, that’s a colossal sum.
Could the police arrest this person for any illegal activity on the darknet? In theory, yes. But if we think realistically, such an assumption would seem unlikely because DNStats keeps operating.
Back then, DeepDotWeb was still free. For many people, marketplace referral links from this site served as a source of income. After DeepDotWeb was shut down, quite a few sites that had made money on such links had to stop their operations as well.
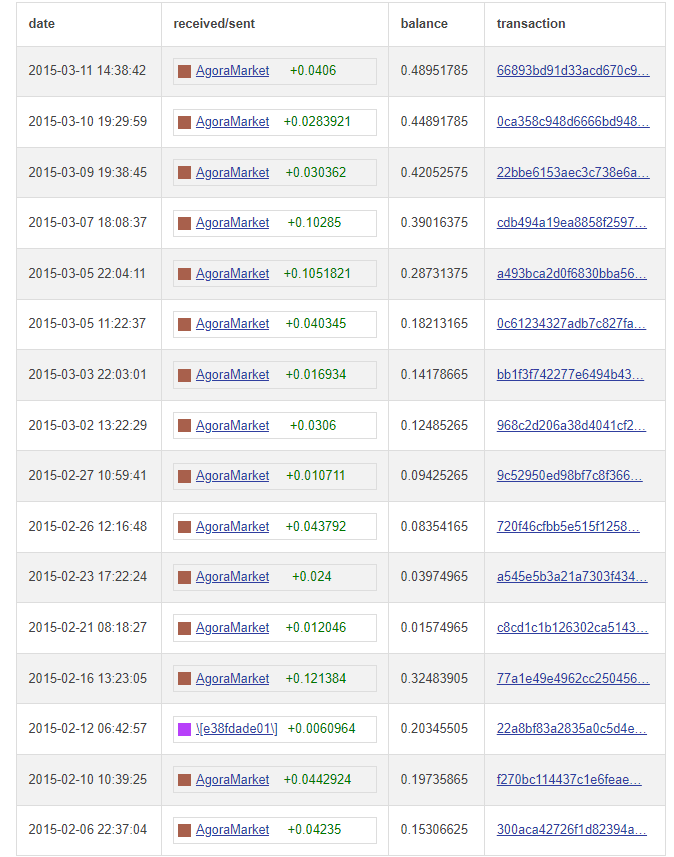
According to one of the most popular versions, the DNStats administrator might have known or guessed what would happen to DeepDotWeb. He or she realized that DNStats would face the same fate. It was rather obvious that the DNStats administrator relied on affiliate links. Data from the blockchain can easily prove that.
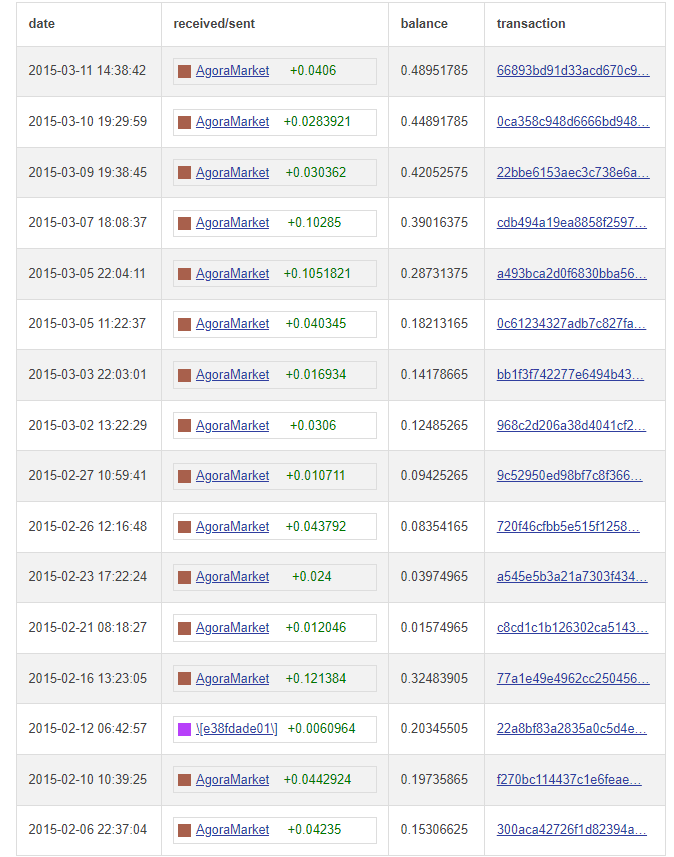
— WalletExplorer
In October 2018, the site announced the launch of Masterlist. During that troublesome transition period, no other relevant pieces of news went live. Some suspicious individuals might think that DNStats and Masterlist were somehow connected — but there is no evidence for this conjecture.
Others might even link DNStats to Olympus Market that exit scammed in Autumn 2018 as well. Yet again, no one can offer any evidence to back up this speculation.
So we can just take it for granted that the initial administrator left DNStats. He or she might have sold the domain deliberately. Otherwise, a third party might have seized the domain. No one seems to know for sure what happened exactly.
The last solid fact we know is that the original DNStats admin kept on tweeting systematically until July 2018. Then, the only thing we can do is to ask questions.
- What happened between that last tweet and the day when they used their BTC wallet for the last time?
- Why didn’t the admin delete their Reddit account immediately but waited for months to do it? That account contained his or her private data.
Can some of our readers shed light on these mysterious events? If yes, feel free to get in touch with us! We’ll be glad to listen to your version.